Understand the Role of Identity Management in a Changing World
Change is a fact of life for employees in every organization — no matter the industry in which they serve. While some changes such as virtualization and web conferencing have been a boon for business leaders, other changes have had the opposite effect. Here are four challenges many organization decision-makers face today, thanks to changes in the business world:
Challenge 1: High employee turnover
 Long gone are the days of employees working for one organization for many years. These days, employees stay in positions an average of only about four years, according to the U.S. Bureau of Labor Statistics. High employee turnover can make managing user accounts and related access more challenging.
Long gone are the days of employees working for one organization for many years. These days, employees stay in positions an average of only about four years, according to the U.S. Bureau of Labor Statistics. High employee turnover can make managing user accounts and related access more challenging.
Managing user accounts is difficult in and of itself. To protect your business, you need to have an identity management system that lets you:
- Securely provision new user accounts. When creating new user accounts, make sure new employees have appropriate access privileges. Not giving employees access to necessary resources will hamper their abilities to perform their jobs. Giving employees too many privileges can leave the organization vulnerable to insider security threats.
- Easily change user accounts when needs arise. For example, you need to be able to change access privileges when you promote employees.
- Quickly delete user accounts when employees leave. It’s important to delete user accounts immediately after employees leave to avoid security risks associated with their ongoing abilities to access your resources.
- Effortlessly manage user accounts for other types of users. It’s not uncommon for contractors, vendors, partners, and customers to have user accounts.
Challenge 2: Increasing mobile device use
 In the past, each employee typically used only one PC to do her or his job. Nowadays, employees might also use company-provided laptops, tablets, smartphones, and other devices to check emails and perform work-related tasks.
In the past, each employee typically used only one PC to do her or his job. Nowadays, employees might also use company-provided laptops, tablets, smartphones, and other devices to check emails and perform work-related tasks.
Allowing employees log into your network with different devices has its advantages. For example, it can lead to increased productivity. However, it also makes managing user authentication more challenging. Besides resetting passwords for employees who forget them, you must deal with other situations, including
- employees logging in from locations that might not offer the same security as your in-house network;
- company-provided mobile device theft or loss; and
- employees trying to log into your network using their own personal computing devices.
Challenge 3: Off-premise applications
Business leaders have always used a variety of applications to run their operations. However, chances are some of those applications are no longer on-premise. In fact, 89% of IT professionals who responded to a RightScale survey report their businesses run at least one application in a public or hybrid-public cloud. However, it’s more difficult to monitor and manage employees’ access to Software as a Service (SaaS) solutions applications.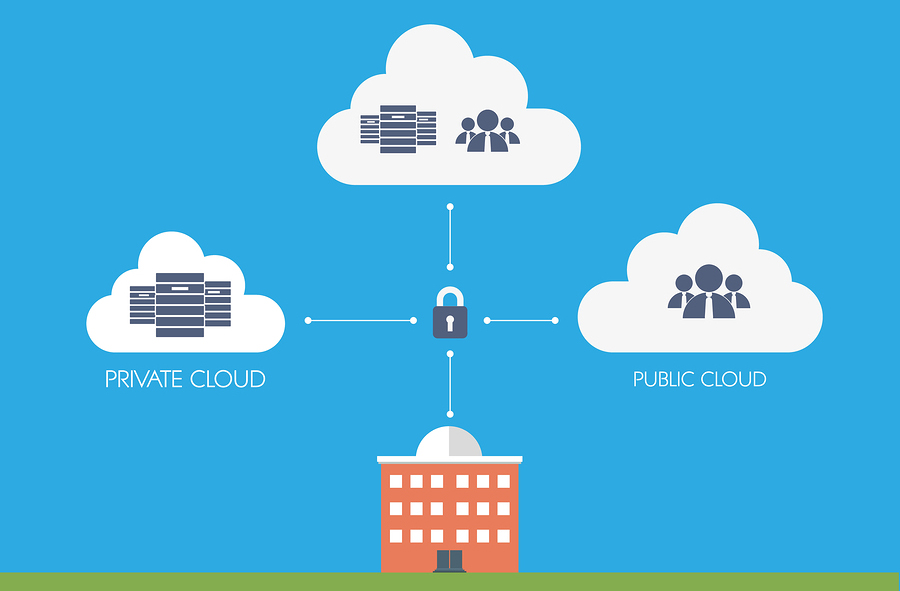
Challenge 4: Data breaches
Data breaches have become a real threat to organization leaders. Since Identity Theft Resource Center personnel began tracking data breaches in 2005, there have been more than 6,700 documented breaches involving more than 885 million records. Plus, many more data breaches likely occurred but went unreported.
 With the data breach threat looming, you need a directory services management solution that will secure your sensitive data yet make it available when necessary.
With the data breach threat looming, you need a directory services management solution that will secure your sensitive data yet make it available when necessary.
You don’t have to face the challenges alone
Although you can’t stop these changes, you can take measures to face the challenges they present — and you don’t have to face them alone. Arisant experts can handle your identity management and access control challenges so you can concentrate on running your business.
Using Oracle Identity Management solutions, Arisant professionals can securely manage the entire life cycles of all your user accounts from creation to deletion. Plus, with the single sign-on system, your users will be able to apply one set of credentials to access all your applications and systems from any authorized device from any location. And the directory services management solution will give you peace of mind knowing your sensitive data is protected, readily available, and compliant with regulations and standards.
[cta]To learn more about how Arisant experts can help you prepare for or avoid these security challenges, contact Arisant at 303-330-4065 or by email at sales@arisant.com.[/cta]

